BadUSB is one of the most concerning USB attack vectors: a malicious device that impersonates a keyboard, network adapter, or other trusted peripheral to execute commands on your computer the moment it’s plugged in. Understanding this threat helps you choose safer hardware and adopt better USB hygiene.
What Is a BadUSB Attack?
Every USB device has a controller chip with firmware that tells the host computer what type of device it is. A BadUSB attack reprograms this firmware so a flash drive announces itself as a keyboard (or other HID device) and types pre-programmed commands at machine speed.
Because the computer trusts keyboards implicitly, these commands execute without any security prompt. A BadUSB device can:
- Open a terminal and download malware
- Exfiltrate files to a remote server
- Create new admin accounts
- Disable security software
- Install persistent backdoors
The attack works on Windows, macOS, and Linux. It’s not a software vulnerability — it exploits the fundamental trust model of USB.
Why Standard Flash Drives Are Vulnerable
Most USB flash drives use generic controller chips (Phison, SMI, Alcor Micro) with firmware that can be reflashed using freely available tools. An attacker who has physical access to a drive — even briefly — can reprogram its firmware without leaving visible traces.
This means:
- A “found” USB drive in a parking lot could be a BadUSB device
- A borrowed drive returned to you could have been reprogrammed
- A supply-chain intercepted drive could be compromised before it reaches you
Choosing Safer Flash Drives
Look for Firmware-Locked Controllers
Some USB drives use controllers with signed, read-only firmware that can’t be reprogrammed:
- Kingston IronKey series — firmware is digitally signed and locked at the factory
- Apricorn Aegis series — hardware-encrypted with locked firmware
- iStorage datAshur series — FIPS-certified with firmware protection
These drives are more expensive, but they eliminate the BadUSB vector.
Consider Hardware-Encrypted Drives
Hardware-encrypted USB drives with on-device authentication (keypads, biometrics) typically have locked firmware as part of their security certification. They solve two problems at once: data encryption and firmware integrity.
For a detailed comparison of hardware vs. software encryption on USB, see our guide on hardware vs. software encrypted drives.
Avoid Cheap, Unbranded Drives
Budget USB drives from unknown manufacturers are most likely to use reflashable controllers with minimal security. For drives that will hold sensitive data or be used in security-sensitive environments, spend more for reputable brands with firmware protection.
Protective Measures on Windows
Even with safe hardware, good USB practices reduce risk:
1. Disable USB Auto-Run
Windows no longer auto-runs programs from USB drives by default (that was fixed years ago), but verify:
Settings → Bluetooth & devices → AutoPlay → Set to "Take no action"
2. Use USB Device Control Policies
Windows 11 Enterprise supports device installation restrictions via Group Policy:
Computer Configuration → Administrative Templates → System → Device Installation → Device Installation Restrictions
You can whitelist specific USB vendor/product IDs and block everything else.
3. Monitor for Unexpected HID Devices
If you plug in a USB flash drive and Windows reports a new keyboard or network adapter, that’s a red flag. Legitimate flash drives announce as mass storage devices only.
4. Use a USB Data Blocker
When charging from untrusted USB ports (airports, hotels), use a USB data blocker (also called a “USB condom”) that physically disconnects the data pins, allowing only power to flow.
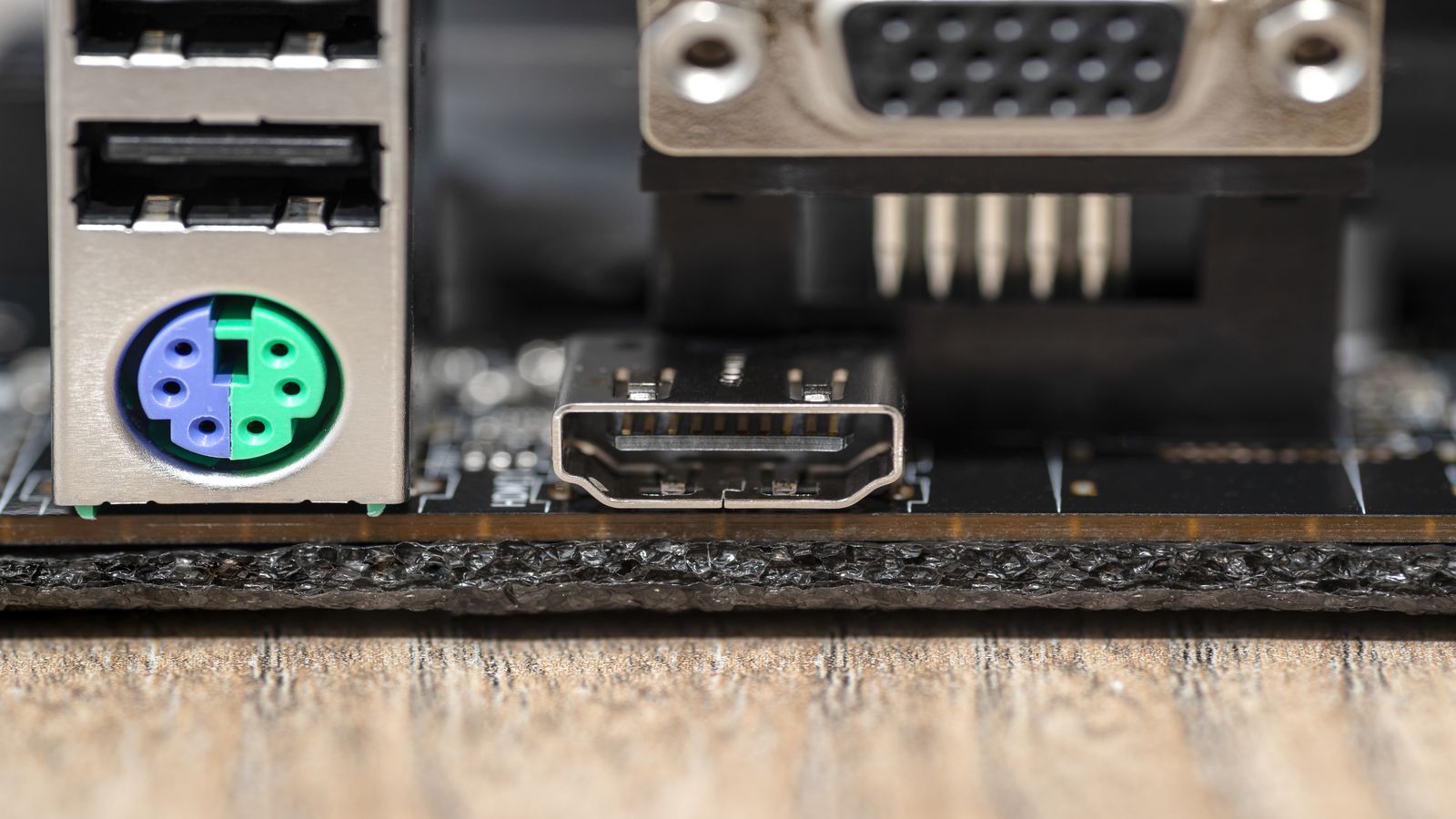
What About USB-C?
USB-C doesn’t change the BadUSB threat. The attack exploits the USB protocol, not the connector shape. USB-C drives are equally vulnerable if their firmware is reflashable.
However, USB-C with USB4 authentication (based on USB-IF’s authentication specification) is starting to appear in enterprise hardware, allowing the host to verify the device’s identity cryptographically before trusting it. This is promising but not yet widespread in consumer hardware.
Practical USB Safety Checklist
- Never plug in found USB drives — this is the oldest social engineering trick in the book
- Buy drives from reputable vendors with firmware protection
- Encrypt sensitive data on USB drives — even if BadUSB isn’t a concern, theft is. See Secure USB Drives
- Verify new software downloads with checksums before transferring via USB — How to Verify Checksums
- Use dedicated drives for sensitive transfers; don’t share drives casually between environments
- Monitor device manager when plugging in USB devices; unexpected device types are suspicious
Key Takeaways
BadUSB is a real but manageable threat. You don’t need to stop using USB drives — you need to be selective about which drives you trust and maintain good USB hygiene. For most users, buying reputable hardware-encrypted drives and never plugging in unknown devices covers the practical risk.
Further Reading
- NIST SP 800-124 — Managing Mobile Devices — Guidelines for removable media
- CISA — Using caution with USB drives — Government USB safety guidance
- USB-IF — USB Authentication Specification — Cryptographic device authentication
- SRLabs — BadUSB research — Original BadUSB disclosure